CapLoader 1.9.7 Released

A new release of CapLoader has been published! Some of the changes can be seen directly in the user interface, such as Community ID values for flows and a few other new columns in the Flows and Services tabs. Other improvements are more subtle, like improved detection of remote management protocols and malicious C2 protocols.
User Interface Improvements
The most important user interface update is probably the addition of a
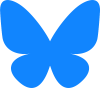
CapLoader now has a column named Retransmissions in both Flows and Services tab, which shows an estimate of how many percent of the packets in each flow or service that are retransmissions. This value can be used to quickly diagnose a network issue without having to inspect network traffic on a packet-by-packet level.
We have also added a column named
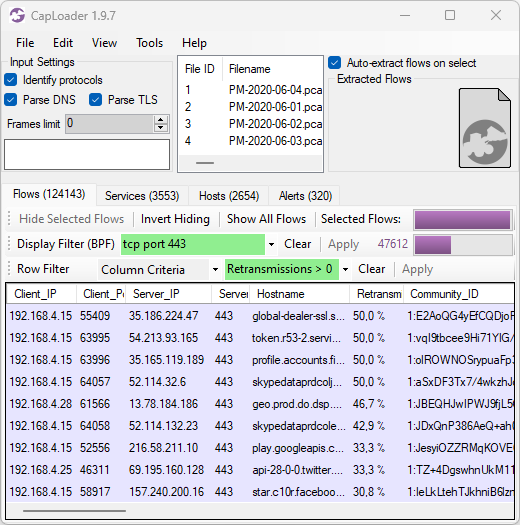
The Severity and
We have also included a handy little feature that allows you to append additional PCAP files to an existing analysis session simply by holding down Ctrl while drag-and-dropping another capture file onto CapLoader. The “Append File(s)” option is also available under CapLoader’s File menu.
Even More Protocols Identified
CapLoader’s unique ability to identify protocols regardless of port has been improved and we’ve also added detections for several new protocols. For this release we’ve focused adding detection for remote monitoring and management (RMM) protocols, such as ConnectWise (formerly ScreenConnect), AnyDesk, NetSupport (including NetSupport RAT), TeamViewer (including TVRAT) and RMS (Remote Utilities). This enables CapLoader to alert whenever an RMM protocol is detected.
We’ve also added detection of several new malware protocols, including Matanbuchus, Meduza Stealer, SectopRAT, STRRAT and zgRAT.
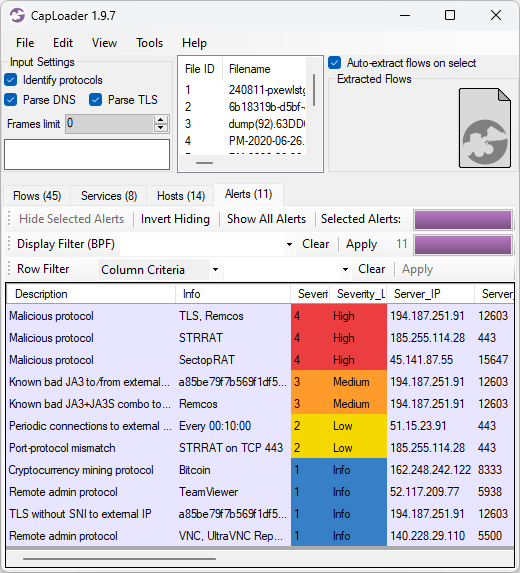
Even More Protocols Decapsulated
CapLoader already decapsulates flows inside of GRE, VXLAN and CapWap. With this release we add support for decapsulation of Teredo, GTP-U, TZSP as well as IP-in-IP traffic, so that tunneled traffic can be analyzed without any additional effort.
Credits
I would like to thank Jarmo Lahtiranta for the TZSP idea and Lenny Hansson for pointing out the need for improved protocol detection. I would also like to thank Christian Kreibich and his fellow Corelight devs for creating and open sourcing the Community ID project.
Updating to the Latest Release
Users who have already purchased a license for CapLoader can download a free update to version 1.9.7 from our customer portal or by clicking “Check for Updates” in CapLoader’s Help menu.
Posted by Erik Hjelmvik on Friday, 06 September 2024 09:45:00 (UTC/GMT)