Erik Hjelmvik
,
Tuesday, 25 October 2016 08:45:00 (UTC/GMT)
NSA's QUANTUM INSERT attack is probably the most well-known TCP packet injection attack due to the
Snowden revelations regarding how GCHQ used this method to hack into Belgacom.
However, the “Five Eyes” are not the only ones who perform this type of attack on the Internet.
We now release a tool to help incident responders to find these types of packet injection attacks.

I had the opportunity to attend and present at SharkFest Europe last week.
My presentation, titled “Dissecting Man-on-the-Side Attacks”,
showed how TCP packet injection attacks can be analyzed if they have been recorded in a packet capture.
In my talk I used a python script called “finject.py”,
which reads PCAP files to find TCP packets with duplicate sequence numbers but different content.
This script has previously only been shared with vetted parties,
but as of my SharkFest presentation findject is now freely available for everyone.
Findject is not the first tool made available to detect TCP content injection attacks.
Other detection methods include Suricata's reassembly_overlap_different_data alert,
Fox-IT's Bro policy to check for inconsistencies in the first packet with payload,
David Stainton's HoneyBadger and
Martin Bruse's qisniff.
Even though these are all great solutions we found that some of them didn't detect all TCP content injection attacks while others gave
too many false positives. We also wanted to have a tool that was fast, portable and simple to use.
This led us to create our own TCP injection detection tool.
python findject.py /nsm/pcap/live/*
opening /nsm/pcap/live/ppp0.150922_192034.pcap - no injections
opening /nsm/pcap/live/ppp0.150923_081337.pcap
PACKET INJECTION 42.96.141.35:80-192.168.1.254:59320 SEQ : 402877220
FIRST :
'HTTP/1.1 403 Forbidden\r\nServer: Beaver\r\nCache-Control: no-cache\r\nContent-Type: text/html\r\nContent-Length: 594\r\nConnection: close\r\n\r\n<html>\n<head>\n<meta http-equiv="Content-Type" content="textml;charset=UTF-8" />\n <style>body{background-color:#FFFFFF}</style> \n<title>TestPage</title>\n <script language="javascript" type="text/javascript">\n window.onload = function () { \n document.getElementById("mainFrame").src= "http://batit.aliyun.com/alww.html"; \n }\n</script> \n</head>\n <body>\n <iframe style="width:860px; height:500px;position:absolute;margin-left:-430px;margin-top:-250px;top:50%;left:50%;" id="mainFrame" src="" frameborder="0" scrolling="no"></iframe>\n </body>\n </html>\n\n'
LAST :
'HTTP/1.1 200 OK\r\nContent-Type: text/html\r\nContent-Length: 87\r\nConnection: close\r\n\r\n<html><head><meta http-equiv="refresh" content="0; url=\'http://id1.cn/\'"></head></html>'
opening /nsm/pcap/live/ppp0.150923_115034.pcap - no injections
opening /nsm/pcap/live/ppp0.150924_071617.pcap - no injections
In the example execution above we can see that findject.py detected an injected TCP packet in the file
ppp0.150923_081337.pcap, while the other analyzed files contained no injections.
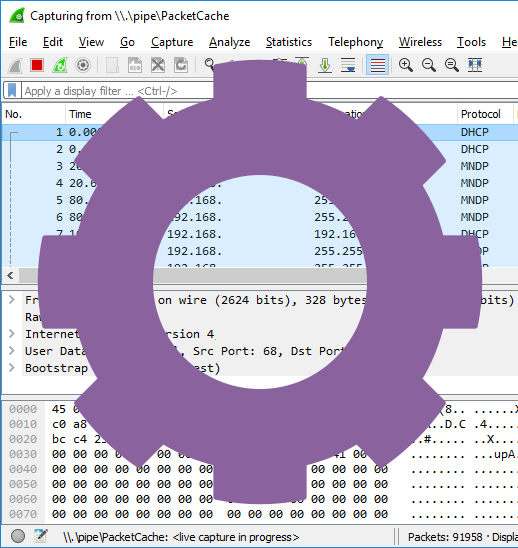
The application layer data of the two conflicting TCP segments are printed to standard output with a header
indicating whether the segment was the FIRST or LAST one. To find out which segment is the real one and which was
the injected one we need to open the PCAP file in either Wireshark, tshark or CapLoader.
tshark -r /nsm/pcap/live/ppp0.150923_083317.pcap -Y "ip.src eq 42.96.141.35 and tcp.port eq 59320" -T fields -e frame.number -e ip.src -e ip.dst -e tcp.seq -e tcp.len -e ip.id -e ip.ttl -o "tcp.relative_sequence_numbers: false"
14 42.96.141.35 192.168.1.254 402877219 0 0x00002e36 94
25 42.96.141.35 192.168.1.254 402877220 726 0x00000d05 70
27 42.96.141.35 192.168.1.254 402877220 726 0x00000d05 69
28 42.96.141.35 192.168.1.254 402877220 170 0x00002e3e 94
The tshark execution above reveals that three packets sent from the web server's IP (42.96.141.35)
are carrying data and have the same sequence number (402877220). Packet 25 and 27 are actually identical,
while packet 28 is smaller (170 bytes) and has a different payload.
The first displayed frame in the tshark output above is the SYN+ACK packet from the TCP 3-way handshake.
So how can we determine which of packets 25, 27 and 28 are real verses injected?
Look at the IP-ID and IP-TTL values!
Frame 28 has IP-ID and TTL values in line with what we see in the TCP 3-way handshake (TTL=94, IP-ID=0x00002e3e),
which implies that this packet is probably authentic. Frames 25 and 27 on the other hand deviate from what we would expect from the server, which tells us that these packets were likely injected (spoofed) into the TCP session through a “man-on-the-side” attack.
To learn more about findject.py and download the tool, please visit:
https://www.netresec.com/?page=findject
Example captures containing TCP content injection attacks can be found on our
Publicly Available PCAP Files page under the
“Packet Injection Attacks / Man-on-the-Side Attacks” section.
You can also read our blog posts Covert Man-on-the-Side Attacks and Packet Injection Attacks in the Wild to learn
more about TCP packet injection attacks.
Posted by Erik Hjelmvik on Tuesday, 25 October 2016 08:45:00 (UTC/GMT)
Tags:
#Netresec
#PCAP
#packet injection
#find
#python
#SharkFest